Looking for the bad guy's needle in a data haystack
 |
| Finding evidence of computer crime can be like looking for a needle in a haystack, as seen in this image from the Fermilab Education Office website. |
When the laboratory has a computer security incident, the incident response and computer security teams must dig through mountains of data. How do they find the little bits that lead to the tracks that the bad guy left behind?
It's a proverbial needle in a haystack. The Splunk software system can help find it.
Computer system managers give the teams the machines' log files before an incident happens. By adding those files to the Splunk software system, the teams can determine the machines' normal behavior. The teams can get a virtual picture of the existing data haystack they would need to search through in the event of trouble.
The system, which can add some 200 gigabytes a day, only shows computer security personnel what they want to see.
This allows them to detect abnormalities. Early detection of suspicious computer activity lets the teams remove suspect computers from the network, containing the damage more quickly.
All laboratory devices are subject to potential security incidents. By using Splunk, computer security personnel can detect the targets of malicious activity to assess the biggest risks, limit them and help contain problems quickly.
-- Tim Rupp, computer security staff
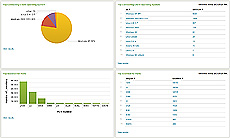 |
| A screen snapshot of some of the information Splunk provides about log files. |
Safety Tip of the Week Archive |